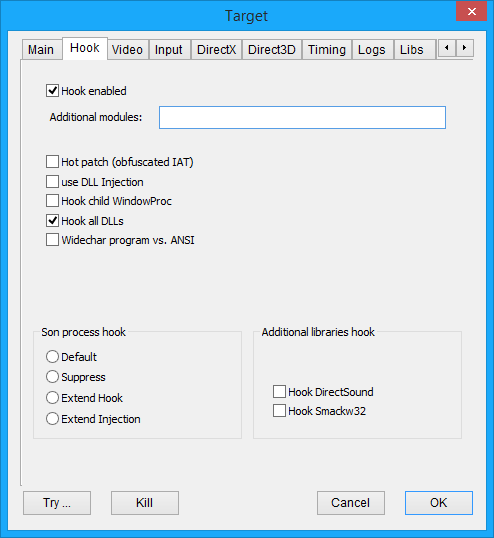
Hook enabled |
HOOKENABLED |
If this flag is not set, DxWnd ignores the task - see gray icon |
Additional modules: |
DxWnd's hooking logic may not notice some DLLs. In these fortunately rare cases, you can fix the issue by entering one or more module names to be added to DxWnd's search algorithm. |
|
Hot patch (obfuscated IAT) |
HOTPATCH |
The original DxWnd used IAT patching to redirect API calls to the altered routines. This method has its advantages, but fails when not all API are reached because they are located in unconnected dlls, referenced by ordinal number or referenced by programs with obfuscated IAT. IAT obfuscation is a sophisticated but common enough technique to make hacker's life harder: for instance, the game executable of Doom III has an obfuscated IAT. Checking this flag cause DxWnd to use an alternate patching technique, that is the "hot patching" that creates a detour assembly code right at the beginning of the API implementation. Once done EVERY SINGLE CALL gets intercepted no matter from where the call is made, but it isn't always possible to apply this technique. Luckily, in the vast majority of cases, they both work. |
Use DLL injection |
STARTDEBUG |
The basic hook thecnique intercepts the first window creation event. At that time, the program may have done unwanted actions already, such as changing video mode or detecting bad conditions or crashing. Checking this flag cause the DxWnd logic to be "injected" right at the beginning of the task execution, making DxWnd able to intercepts all events. The drawback is that this only works when the task is activated from the DxWnd interface – see red icon. Another drawback is that the injection process resembles pretty much of an activation from a debugger, increasing the chances for game protections to intercept this situation and stop the program. |
Hook child WindowProc |
HOOKCHILDWIN |
By default, DxWnd intercepts the WindowProc routine of the main window, and this is enough for its purposes. In some cases, though, this is not enough and this flag tells DxWnd to intercept and redirect the WindowProc routines of all child windows as well. |
Hook all DLLs |
HOOKDLLS |
The original DxWnd behaviour was limited to search & hook calls made by the main program directly. Checking this flag cause DxWnd to recurse in all non-system DLLs address space to hook calls there. It's necessary in all cases where the graphic engine is not directly coded in the program, but it's implemented in a separated engine DLL. |
Widechar program vs. ANSI |
ANSIWIDE |
DxWnd uses ANSI versions of several system calls by default. This flag tells DxWnd to use the corresponding WIDECHAR version instead. |